Your organizational leadership team should be aware of the compliance requirements they need to fulfill in order to conduct their operations. In addition to CMMC, your company should take the time to learn about these other important compliance standards and regulations to both improve and secure your operations and also be more accessible to new business opportunities.
Here is a list of important compliance requirements with specific information on each in the section below.
NIST & DFARS
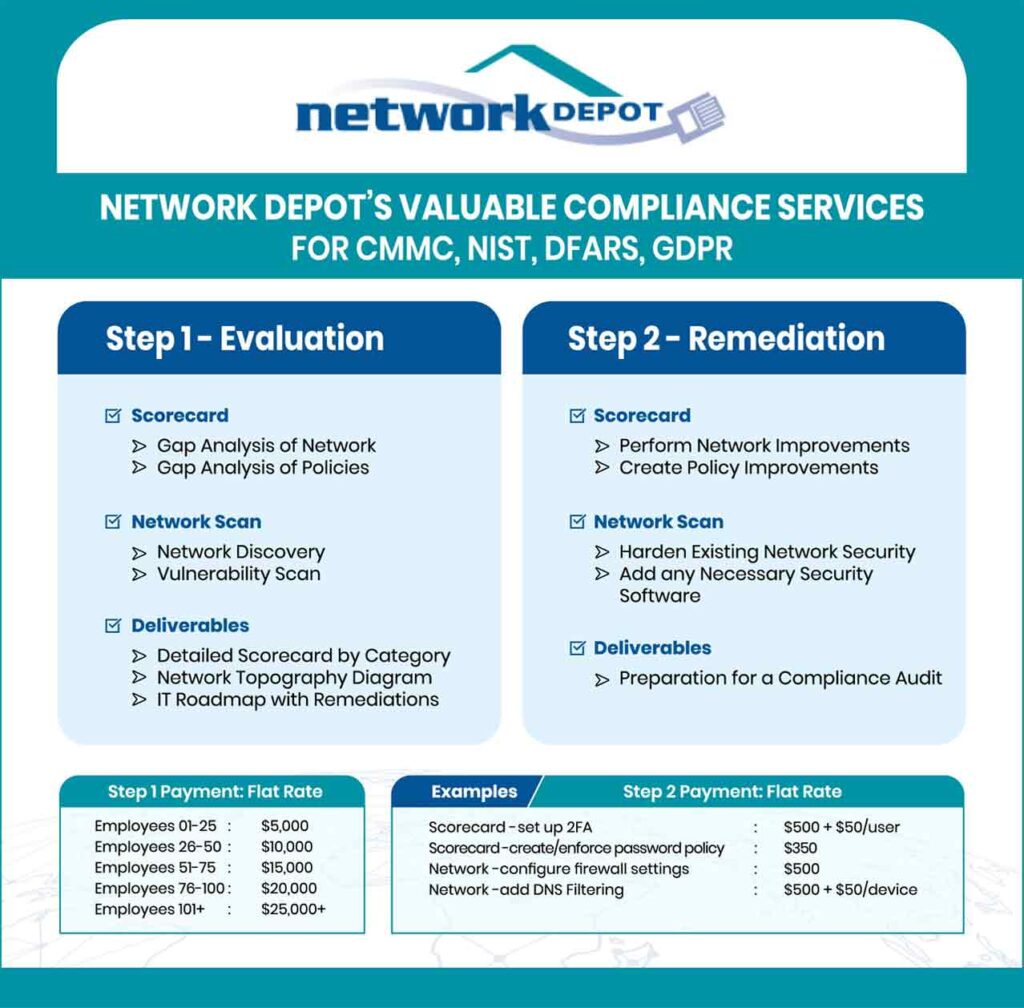
The National Institute of Standards and Technology (NIST) issues cybersecurity controls for companies to follow when working on government contracts. The NIST security mandate that is most relevant to small businesses is NIST Special Publication 800-171. This mandate was introduced in 2017, with important revisions in 2020, and details the security compliance requirements for any company that processes, stores, or transmits potentially sensitive information for the DoD, General Services Administration (GSA), and other federal and state agencies. For the first time via NIST 800-171, IT security compliance requirements apply to any companies working in the federal supply chain including prime contractors, subcontractors supporting prime contractors, and subcontractors working for other subcontractors.
In 2015 the DoD published a FAR (Federal Acquisition Regulations) supplement referred to as the Defense Acquisition Federal Regulation Supplement (DFARS). This regulation supplement was issued to emphasize the importance of maintaining cybersecurity standards according to requirements laid out by NIST SP 800-171. All private contractors working with the DoD must be DFARS-compliant and show proof of this for all contracts moving forward.
HIPAA/HITECH
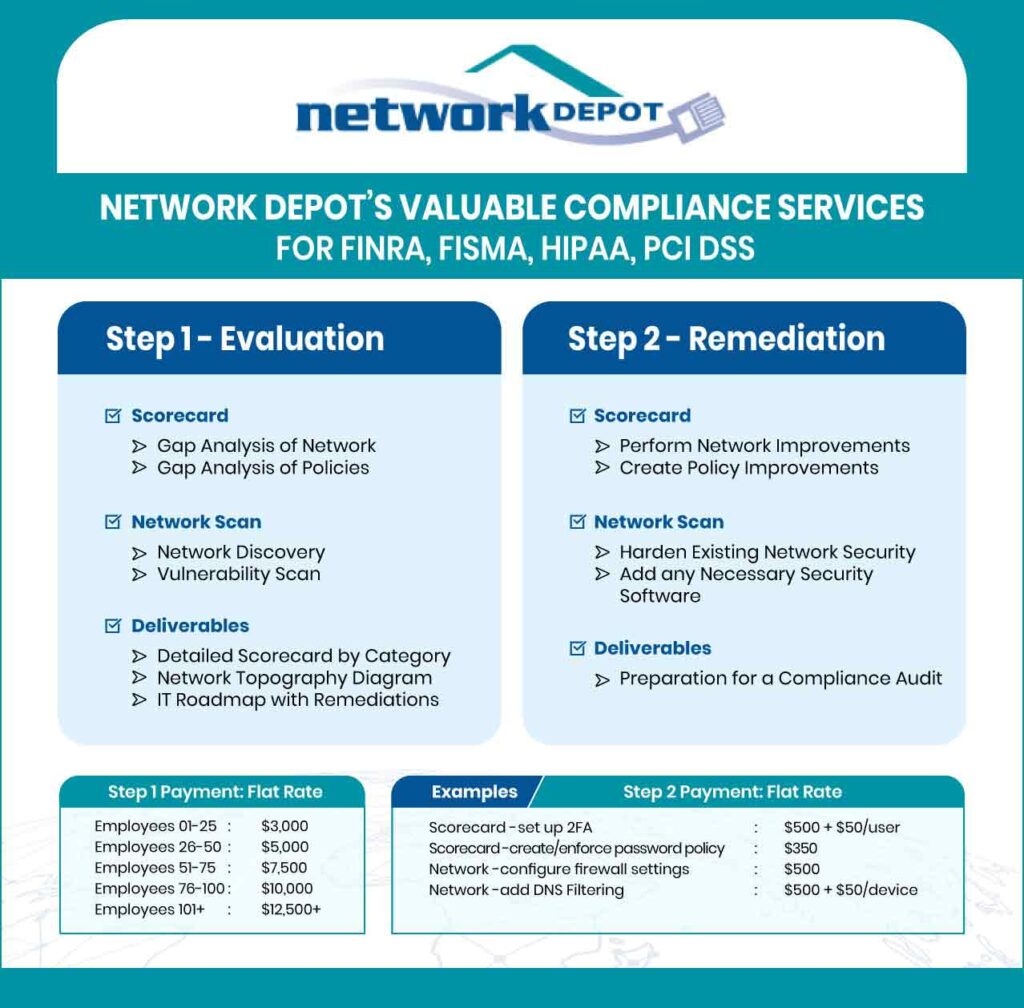
The Health Insurance Portability and Accountability Act (HIPAA) was passed in 1996 to improve the nation’s health care system by mandating the standards-based implementation of security controls by all health care entities that create, store, or transmit personal health information (PHI). This act also applies to any companies that work with any of this sensitive information such as law firms, accountants, billing services, IT companies, and other professional service providers.
The Health Information Technology for Economic and Clinical Health Act (HITECH) was part of the American Recovery and Reinvestment Act of 2009. Its passage built upon the standards in HIPAA bringing additional compliance requirements to organizations involved with health care. HITECH mandates healthcare organizations and business associates to apply “meaningful use” of security technology to ensure the confidentiality, integrity, and availability of protected personal data in electronic, paper, or oral form. It also requires that companies notify their customers and clients about any data breach.
GDPR
The European Union’s General Data Protection Regulation (GDPR) came into effect in May 2018 requiring businesses to provide significant privacy protections for consumers in the European Union. Importantly, this impacts any US companies that collect any money from EU consumers or target them with marketing efforts. This regulation also applies to any US companies, which have a web presence accessible within the EU that collects personally identifiable data (PII) such as email addresses, phone numbers, and home addresses. Some industry sectors that are likely to fall under this regulation include tourism, software services, travel, hospitality, and e-commerce companies.
Some of the required steps companies must take to comply include ensuring customer content to obtain their personal data, protecting sensitive customer data, adding a designated data protection officer, and providing notification of data breaches within 72 hours of a successful cyberattack.
PCI DSS
One set of information security standards that virtually all businesses have to follow is the payment card industry data security standard (PCI DSS). The major branded credit cards mandate that any businesses that accept payment with their products follow these standards. These requirements seek to ensure that all companies that process, store, or transmit sensitive credit card information maintain it securely.
This security standard has 12 requirements that revolve around practicing good cyber hygiene including having updated firewalls and configured passwords and settings as well as the encryption of the transmission of cardholder data across public networks. It also requires strict limits on employees having access to workplace and cardholder data along with regular monitoring and testing of your network defenses.
Additional Information on Compliance Regulations
Here are some links to articles we have written about important compliance regulations that may be relevant to your organization.
https://www.networkdepot.com/important-compliance-requirements-for-your-small-business/
https://www.networkdepot.com/new-cybersecurity-certification-required-for-companies-working-with-the-department-of-defense/
https://www.networkdepot.com/the-importance-of-nist-compliance-for-small-businesses/
https://www.networkdepot.com/hipaa-and-hitech/
https://www.networkdepot.com/the-impact-of-covid-19-on-hipaa/
https://www.networkdepot.com/gdpr-small-business-impact/
https://www.networkdepot.com/resource-center/understanding-it/understanding-pci/
https://www.networkdepot.com/finra/
https://www.networkdepot.com/cipa-compliance-grants-tech-discounts/